Three CRA Scenarios: What the Cyber Resilience Act Means for Your Business
- March 2, 2026
- 0
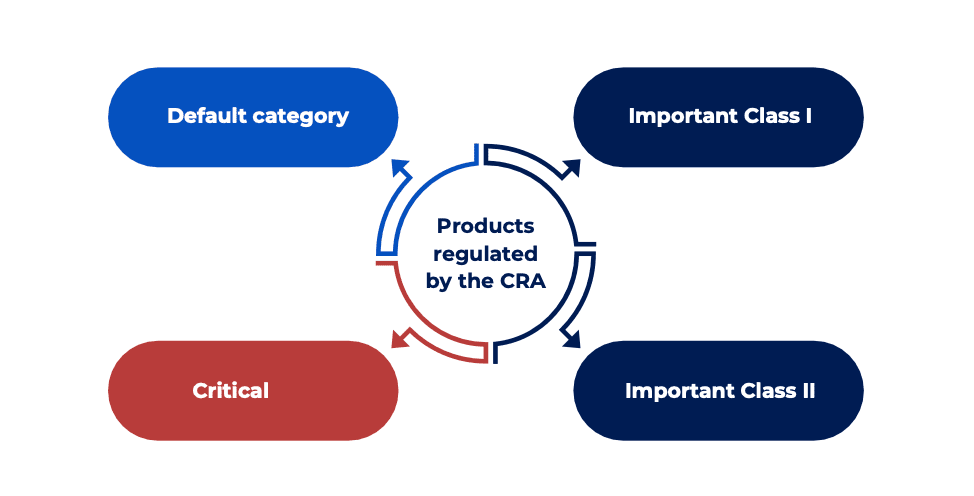
The EU Cyber Resilience Act (CRA) casts a wide net over products with digital elements sold in the European market. But “wide” doesn’t mean identical treatment for everyone. Your obligations depend on what you build, how you deliver it, and your role in the supply chain.
Below are three realistic business scenarios — and what CRA compliance actually looks like in each case.
Contents
B2B SaaS Startup Launching in January 2027
Profile:
You’re launching a B2B SaaS platform for EU enterprise customers. It runs fully in the cloud and goes live in January 2027.
Are You in Scope?
It depends on architecture.
You’re generally not in scope if:
-
Your software runs entirely on your infrastructure
-
Customers access it via browser or API only
-
Nothing is installed locally
You are in scope if:
-
You distribute a desktop agent, browser extension, or mobile app
-
Your SaaS performs remote data processing essential to a connected product (e.g., IoT device backend)
Under CRA, remote processing tied to a product’s core functionality becomes part of that product’s security perimeter.
Timeline Impact for January 2027 Launch
Two key dates matter:
-
September 11, 2026 → Vulnerability & incident reporting obligations begin (24-hour initial report, 72-hour follow-up).
-
December 11, 2027 → Full CRA compliance required (CE marking, conformity assessment, Annex VII documentation, SBOM).
If you launch in January 2027, reporting obligations are already active. A security incident in Q1 2027 means you must already have operational reporting workflows.
What You Should Do Now
-
Clarify scope early — assume you’re in scope if any client-side component exists.
-
Integrate SBOM generation into CI/CD pipelines.
-
Build vulnerability response workflows before launch.
-
Prepare Annex VII technical documentation pre-market.
How SaM Solutions Supports SaaS Startups
Startups face a real tension: ship fast or build compliance infrastructure.
SaM Solutions helps by:
-
Embedding SBOM pipelines into CI/CD
-
Integrating secure SDLC practices into daily development
-
Providing managed vulnerability monitoring
-
Preparing Annex VII documentation aligned to CRA
This allows startups to launch compliant — not scramble after go-live.
Wearable Manufacturer with an EOL Device Still in Use
Profile:
You manufacture smart wearables. Your first-gen device was discontinued in 2024. A second-gen version is now active. Thousands of legacy devices remain in customer hands and still connect to your backend.
Are You in Scope?
Yes — for both devices, but differently.
New device:
Fully subject to CRA from December 2027, reporting obligations from September 2026.
Legacy (EOL) device:
-
Not retroactively subject to full CRA requirements
-
BUT Article 14 reporting obligations apply from September 2026
-
If exploited vulnerabilities impact firmware or backend services, reporting is mandatory
EOL does not mean “exempt.” If the device remains connected, you retain monitoring and reporting responsibilities.
The Backend Risk
If your backend supports both old and new devices:
-
A shared vulnerability triggers obligations across both product lines.
-
Sunsetting hardware while keeping backend access active creates compliance exposure.
Practical Steps
-
Map backend services still serving legacy devices.
-
Decide: maintain securely or decommission.
-
Extend SBOM tracking to legacy firmware.
-
Clearly communicate support periods to customers.
CRA also mandates a minimum 5-year support period from market placement. A 2022 device may require security support until 2027.
How SaM Solutions Supports Wearable Manufacturers
SaM Solutions provides:
-
Embedded firmware security maintenance
-
IoT backend architecture separation (legacy vs current)
-
Continuous CVE-to-product vulnerability monitoring
-
Secure EOL transition planning
This is especially critical for long-lived device ecosystems.
Independent iOS Developer with Ten Apps
Profile:
You’re a solo developer with ten paid iOS apps on the App Store. Most run offline or use public APIs. No backend infrastructure.
Are You in Scope?
Yes.
Mobile apps distributed in the EU fall under the CRA. As the developer placing the app on the market, you are the manufacturer — not Apple.
Your Risk Profile
Lower than hardware manufacturers, but not negligible.
Advantages:
-
Likely default product category (self-assessment allowed)
-
No remote processing infrastructure
-
Reduced financial penalties for SMEs regarding notification delays
Challenges:
-
Each app counts as a separate product.
-
You must monitor third-party libraries.
-
You must provide security updates for at least 5 years.
-
Abandoned apps still on the store remain your liability.
Managing ten apps = managing ten SBOMs and vulnerability lifecycles.
What You Should Do
-
Consolidate: remove apps you won’t maintain.
-
Automate SBOM generation (e.g., Syft).
-
Use dependency monitoring tools (e.g., Dependabot).
-
Clearly document support lifetimes.
-
Prepare minimal Annex VII documentation.
How SaM Solutions Helps Indie Developers
For small teams without compliance staff, SaM Solutions offers:
-
iOS maintenance & security updates
-
Portfolio-wide SBOM management
-
Managed vulnerability monitoring
-
Annex VII documentation support
This keeps apps compliant without overwhelming development time.
Comparison at a Glance
| Scenario | In Scope? | Key Deadline | Core Risk | Support Focus |
|---|---|---|---|---|
| SaaS Startup | Depends on architecture | Sept 2026 (reporting) | Building reporting infra pre-launch | SBOM pipelines, secure SDLC |
| Wearable Manufacturer | Yes | Sept 2026 (reporting) | Legacy + shared backend exposure | Firmware maintenance, IoT segmentation |
| Indie iOS Developer | Yes | Dec 2027 (full compliance) | Managing multiple small products | App maintenance, SBOM service |
Final Takeaway
The Cyber Resilience Act does not treat all businesses equally.
-
A SaaS startup faces early reporting pressure.
-
A hardware manufacturer must manage legacy exposure.
-
An indie developer must scale compliance across limited resources.
What they share is this:
September 2026 arrives before December 2027.
Reporting infrastructure must be operational well before full compliance kicks in.
The smartest approach isn’t overengineering compliance — it’s aligning effort with your real exposure profile.
The right engineering partner helps you build proportionate, scalable compliance systems that match your product architecture — without slowing innovation.